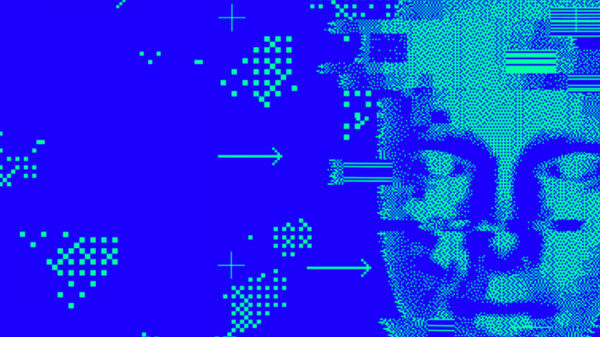
Sophos, a leader in next-generation cybersecurity, recently released new findings on the Tor2Mine cryptominer, “Two flavors of Tor2Mine miner dig deep into networks with PowerShell, VBScript,” that show how the miner evades detection, spreads automatically through a target network and is increasingly harder to remove from an infected system. Tor2Mine is a Monero-miner that has been active for at least two years.
In the research, Sophos describes new variants of the miner that include a PowerShell script that attempts to disable malware protection, execute the miner payload and steal Windows administrator credentials. What happens next depends on whether the attackers successfully gain administrative privileges with the stolen credentials. This process is the same for all the variants analyzed.
For example, if the attackers manage to get hold of administrative credentials, they can secure the privileged access they need to install the mining files. They can also search the network for other machines that they can install the mining files on. This enables Tor2Mine to spread further and embed itself on computers across the network.
If the attackers cannot gain administrative privileges, Tor2Mine can still execute the miner remotely and filelessly by using commands that are run as scheduled tasks. In this instance, the mining software is stored remotely rather than on a compromised machine.
The variants all attempt to shut down anti-malware protection and install the same miner code. Similarly, in all cases, the miner will continue to re-infect systems on the network unless it encounters malware protection or is completely eradicated from the network.
“The presence of miners, like Tor2Mine, in a network is almost always a harbinger of other, potentially more dangerous intrusions. However, Tor2Mine is much more aggressive than other miners,” said Sean Gallagher, senior threat researcher at Sophos. “Once it has established a foothold on a network, it is difficult to root out without the assistance of endpoint protection software and other anti-malware measures. Because it spreads laterally away from the initial point of compromise, it can’t be eliminated just by patching and cleaning one system. The miner will continually attempt to re-infect other systems on the network, even after the command-and-control server for the miner has been blocked or goes offline. As cryptocurrencies continue to increase in value and support the ever-growing ransomware and cyberextortion landscape, we may well see more, and more aggressive, variants of other cryptominers emerge.”
Sophos researchers also discovered scripts designed to kill off a variety of processes and tasks. Almost all of them are related to crimeware, including competing cryptominers and clipper malware that steals cryptocurrency wallet addresses.
“Miners are a low-risk way for cybercriminals to turn a vulnerability into digital cash, with the greatest risk to their cash flow being competing miners discovering the same vulnerable servers,” said Gallagher.
Sophos recommends the following to help organizations protect their networks and endpoints against cryptominers such as Tor2Mine:
- Patch software vulnerabilities quickly on internet-facing systems, such as web applications, VPN services and email servers, as this will make them far less likely to fall victim to cryptominers
- Install anti-malware products – miners are usually easily detected by such technologies – particularly those that leverage Windows’ Anti-Malware Software Interface (AMSI) to spot scripts intended to shut down malware protection
- Monitor for unusually heavy use of processing power, reduced computer performance and higher than expected electricity bills, as any of these can indicate the presence of cryptominers on the network
Sophos detects Tor2Mine variants as the MineJob family (MineJob-A through E) and detects the script behaviors of each variant.
Indicators of compromise for the Tor2Mine variants discussed in the research are available on SophosLabs’ GitHub page.